There is currently no official confirmation of an active EVA community airdrop distributed by the Evanesco Network as of March 2026. If you have seen pop-ups claiming you qualify for free tokens, proceed with extreme caution. Many platforms confuse users with fake opportunities designed to steal wallet access. Before we look at the token itself, it is critical to understand that legitimate projects announce distribution through verified channels. Without a snapshot date or claim period officially published by the team, any site asking for your seed phrase is dangerous.
The Current Status of Evanesco Distribution
Searching through available records and on-chain data from late 2025 reveals very low trading activity for the EVA token. The project operates quietly compared to mainstream cryptocurrencies. While the infrastructure is live, community rewards programs often require significant user base growth before launch. Until you see a formal announcement on their verified social media accounts, treat all rumors as unverified.
| Metric | Value |
|---|---|
| Contract Address | 0xd6cAF5Bd23CF057f5FcCCE295Dcc50C01C198707 |
| Total Supply | 40 Million Tokens |
| Blockchain | Ethereum (ERC-20) |
| Launch Date | May 19, 2021 |
You should bookmark the contract address directly on Etherscan. This allows you to watch transactions independently of marketing noise. If a real event happens, holders will see movement first.
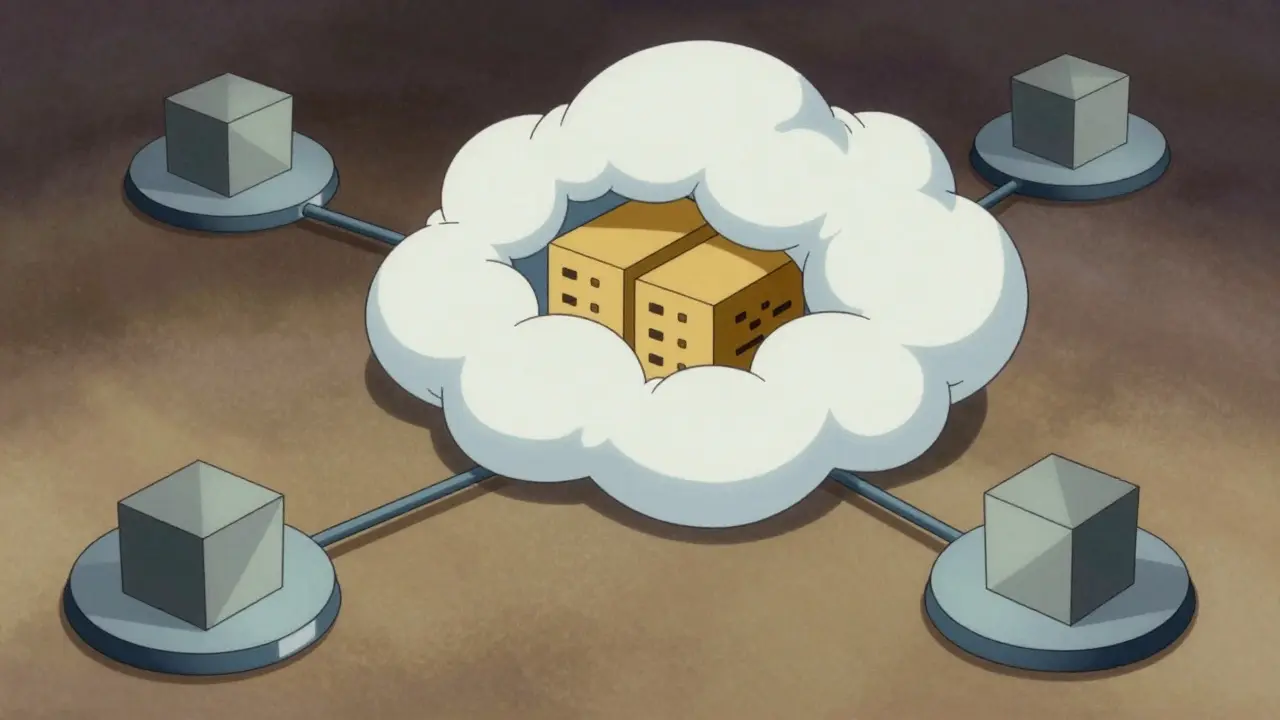
Understanding the Evanesco Network Platform
To understand why an airdrop might happen, you need to know what the project actually does. Evanesco Network is a privacy-focused blockchain platform designed to hide transaction routing details. Unlike standard public chains where every transfer is visible, this system aims for anonymous financial agreements across multiple chains. It was built as an EVM-compatible network, meaning developers familiar with Ethereum tools can work on it easily.
The core technology relies on what they call a Layer0 privacy network. This sits underneath standard applications to ensure data security. They also describe it as middleware for encryption ecosystems. In practical terms, this means businesses wanting private ledgers could use this instead of building their own security from scratch. However, privacy protocols often struggle with adoption because regulators prefer transparency.
How Privacy Protocols Impact Token Value
Privacy coins face unique challenges regarding market valuation. Because anonymity complicates tracking illicit activities, many exchanges avoid listing them. Our search results showed conflicting price data, with some sources reporting zero volume and others showing minimal trade counts. This volatility suggests the token is speculative rather than utility-driven at this stage.
Air drops are usually used to incentivize early adopters to use the network. For a privacy chain, this means using the encrypted routing features. If the network remains inactive, a reward program makes little sense. Most teams distribute tokens when they need gas fees paid by new users or when they need validators securing the chain. Check the network activity before expecting rewards.
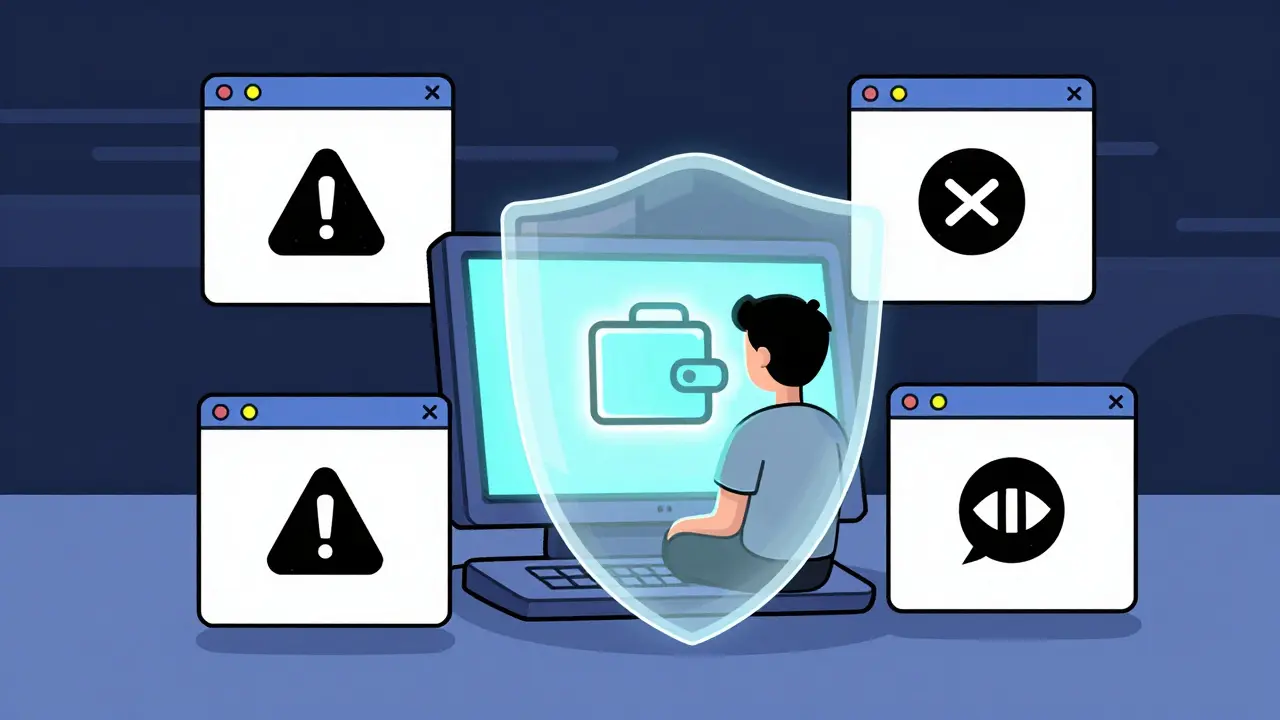
Avoiding Scams Linked to Fake Claims
This is the most vital part of this guide. Since official details are missing, scammers fill the gap with fake landing pages. They create sites looking exactly like official ones, promising you an "EVA airdrop" if you connect your wallet. Here is how to spot the difference:
- Seed Phrase Requests: Legitimate distributions never ask for your recovery phrase. Enter it anywhere, and you lose everything instantly.
- Gas Fee Prepayment: Real airdrops do not require you to send money to receive free money. If you must pay "gas" to claim, it is likely a drain attack.
- Urgency Tactics: Scammers use countdown timers to force panic. Official events give clear dates with hours to prepare.
- DNS Spoofing: Typosquatting URLs (like evansceo.com instead of evanesco.com) are common tricks.
Always verify the domain against the project's official documentation page. If the link was sent via a suspicious DM on Discord or Telegram, assume it is malicious until proven otherwise.
Steps to Monitor Future Announcements
If you hold the token or follow the project, here is the best workflow to stay updated without falling for phishing traps.
- Follow Verified Handles: Look for the blue checkmark on X (Twitter). Ensure the account matches the age of the project (2021 launch).
- Check GitHub Activity: Real development shows up in code repositories. If the last commit was years ago, expect no updates.
- Use Aggregators Carefully: Sites like CoinGecko or DEXTools list listings, but always cross-reference with the smart contract on-chain explorer.
- Monitor Wallet Balance: Keep a hardware wallet separate from your hot wallets used for browsing. Do not keep large amounts in a browser extension wallet.
Setting up notifications for the specific token contract address is safer than relying on third-party news apps. You can configure alerts on blockchain explorers to ping you whenever a new holder receives funds.
Token Utility Beyond Rewards
Even without a current distribution event, understanding the economics helps assess long-term potential. The total supply is capped at 40 million units. There are approximately 2,600 holders recorded on-chain as of late 2025. This creates a fragmented ownership structure where no single entity holds massive dominance, which prevents centralized manipulation but also limits organic momentum.
The token functions as payment for privacy services on the Layer0 network. Users would pay EVA fees to encrypt transactions or utilize the cross-chain gateway. Without active users, the fee revenue remains near zero. Investors often wait for partnerships with larger DeFi protocols to validate these utility claims. Until then, holding the asset carries high risk relative to established networks.
Technical Architecture and Interoperability
The project claims interoperability with external networks and oracles. This is a technical feature that supports cross-chain bridges. Privacy layers on bridges are notoriously difficult to secure because the bridge becomes the single point of failure. If the privacy wrapper fails, transaction history leaks.
Developers working on heterogeneous cross-chain asset agreements need robust encryption. The virtual machine mentioned in their whitepaper is supposed to handle the scaling. If the Virtual Machine is truly compatible with external interfaces, it allows other chains to accept encrypted proofs from Evanesco. This would theoretically solve the zero-knowledge proof bottleneck, but proof-of-concept demos are required to confirm functionality.
Evaluation of Exchange Listings
Listings on major exchanges increase legitimacy. Currently, reports suggest the token is awaiting listing on platforms like KuCoin or OKX. Small caps like this often reside on decentralized exchanges (DEX) initially. Moving to a centralized exchange adds scrutiny.
Regulatory bodies in the United States and Europe have tightened rules around privacy assets. Any future expansion into fiat on-ramps (Apple Pay or Google Pay integration mentioned in earlier data) depends on passing compliance audits. This affects whether a global rollout or community giveaway is feasible.
Strategic Patience for Holders
Waiting for an event like a potential EVA airdrop requires patience and constant vigilance. In the absence of data, speculation drives behavior. Instead of chasing ghosts, focus on capitalizing on the underlying tech if it improves. Check quarterly reports if the team publishes them. Silence from developers often indicates resource constraints rather than planned secrecy.
Engaging with the community forums can sometimes yield insider tips. Look for patterns in governance proposals. Often, airdrops are discussed weeks in advance under different names like "Community Reward Program" or "Liquidity Mining." Translate those buzzwords back into the terminology you are searching for.
6 Comments
The inherent conflict between anonymity features and financial regulations ensures most tokens like this eventually get delisted by centralized exchanges regardless of technical merits
It is really important to check the official links before clicking anything that looks too good to be true online
We all want to make money but staying safe comes first when dealing with crypto wallets
Just stick to the verified social media pages listed in the guide and ignore random messages you get in private chats
Staying patient helps you avoid losing funds to bad actors trying to trick you right now
You guys are ignoring the zk-proof verification methods mentioned in the architecture section completely
If the Layer0 middleware isn't fully audited then the entire transaction routing system is vulnerable to state vector leakage during encryption handshakes
Most teams claim interoperability but fail to deliver secure cross-chain bridges that pass rigorous security standards required by institutional investors
Don't let the marketing hype blind you to the actual solidity code vulnerabilities present in the contract deployment phase
i feel so stressed when i see people losing their life savings to these fake sites it makes me cry :(
we just want to hold our bags safely without worrying about seed phrases being stolen every single day
please everyone stay safe and dont trust anyone asking for keys online :o
my heart hurts for the victims who lose everything so quickly
Just keep your hardware wallet secured away from the internet always!
It gives you peace of mind knowing your assets are offline and safe from remote breaches or phishing attempts targeting browser extensions
Sometimes waiting for the next big update feels slow but it protects us in the long run against unnecessary risks
Stay strong everyone!
The concept of privacy in a digital age remains a complex philosophical dilemma that challenges traditional notions of transparency
When we encrypt transactions we are essentially removing accountability from the public ledger view which creates a tension with societal norms
Many argue that anonymity empowers individuals against authoritarian oversight while others fear it enables illicit market behaviors
This duality exists in every privacy protocol that has attempted to gain widespread adoption over the last decade
Technological solutions can never fully resolve the moral implications embedded within the code itself
Regulators view untraceable funds as a threat to national economic security regardless of user intent
Therefore even robust encryption layers like Layer0 face existential threats from external policy enforcement mechanisms
Developers build these systems hoping for a future where finance is decoupled from identity entirely
Such a utopia requires massive shifts in how governments approach digital asset taxation and reporting
Until those frameworks evolve the survival of tokens like EVA depends on underground demand rather than open exchange listings
Investors often underestimate the human factor involved in maintaining network security over extended periods of time
Trust must be placed in the mathematical guarantees rather than the reputation of the founding team members
History shows that most privacy chains fail due to compliance pressure rather than technical flaws in the cryptography used
We should consider whether the current utility justifies the risk of holding such a high volatility speculative asset
Ultimately the decision rests on individual values regarding financial sovereignty versus community safety standards
The bridge between technical capability and market reality is wider than most white papers admit to us